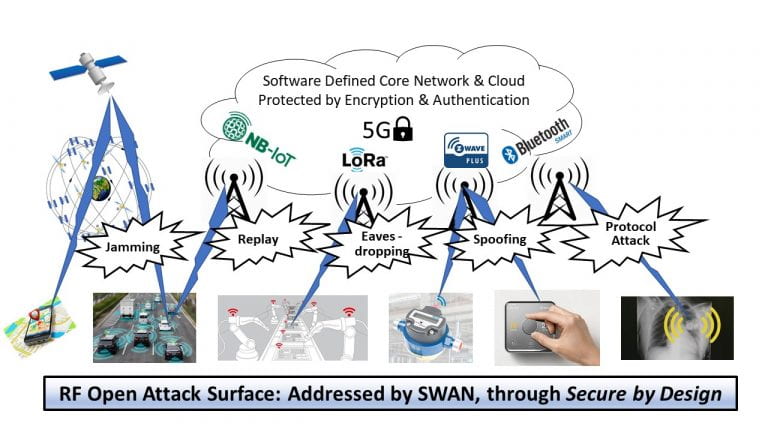
Wireless connectivity is vital to society and any disruption to it could have catastrophic consequences, but there is growing concern that networks are increasingly vulnerable to cyber attack. There have been a number of serious examples in the UK and other countries, where attacks have been mounted for motives ranging from extortion to state subversion. The UK Government’s Secure By Design initiative is intended to ensure that all systems are built on secure foundations.
SWAN’s (Secure Wireless Agile Networks) technology will extend key Secure by Design principles to the radio interface and enable the fundamental parameters and architectures of wireless systems to be:
- Adaptable to new spectrum and interface specifications;
- Resilient against accidental or induced failures (such as jamming);
- Resistant to cyber attack.
SWAN will therefore strengthen the UK's ability to defend its critical infrastructure and bring new secure radio technologies to market, as well as addressing secondary attacks upon wireless simple devices to render large complex installations inoperative (e.g. oil refineries).
Though modern wireless standards incorporate encryption and authentication, the availability of software-defined radio equipment now allows hackers to develop attacks that will not have been considered in the standards’ design. Such attacks could range from simple jamming through to taking over parts of the network. In the worst case, vulnerabilities in mass market mobile phones might be exploited to distribute “RF malware”, for example to jam large numbers of cell sites. It is important to proactively identify and understand these vulnerabilities and develop protective measures, which should ideally include the ability to field-update every aspect of the physical layer radio operation, in line with key principles of secure design.
For the future, a “Secure By Design” mind-set needs to be inculcated into the evolution of standards and the training and education of engineers. Such measures will also be essential to enable spectrum allocation through Dynamic Spectrum Access, thus improving spectrum usage based on instantaneous need in both space and time, rather than fixed licensing.
In the SWAN partnership, GCHQ will play an advisory role in education and technology research and development carried out by Toshiba Europe, Roke Manor Research, and the University of Bristol. Read more about the Project Consortium.
A full overview of the SWAN programme, including the programme background, objectives and research challenges, is available to read in the Introduction to Secure Wireless Agile Networks (SWAN).
Programme Objectives:
- Establish a methodology to understand and synthesize attacks on communications systems vectored through the radio interface
- Develop methods for effective and efficient RF threat detection, analysis and mitigation
- Develop methods to design and implement agile and resilient transceivers
- Develop a testing methodology and resource for radio networks to evaluate threats and mitigations, avoiding the tendency to “group-think” that could exclude various types of attack or defence
- Apply SWAN’s secure agile and robust RF technology to Dynamic Spectrum Access to enhance spectrum utilisation whilst mitigating misuse
- Train SWAN’s academic and industrial team to embed Secure by Design principles in future wireless devices, systems and standards
- Propagate wireless Secure by Design principles to the wider community, including undergraduate and taught postgraduate education
- Engage with the security community by building links with RITICS, PETRAS, NCSC, and other key organisations and networks
